Control panel address
Add new address
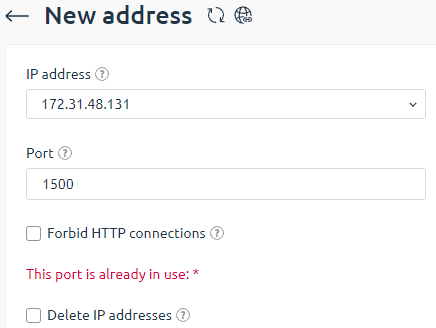
- Go to Settings → Control panel address → Add button.
- Fill in the form fields:
- IP-address — select the IP-address for incoming connections;
Port — enter the port number for incoming connections. Leaving this field blank will apply the default value;
Note:
If you change the port, the panel may become unavailable. Before changing, open the port that you want to assign to the panel in the system firewall rules.
- Forbid HTTP connections — the built-in web-server can receive both HTTP and HTTPS requests. Select the check box to forbid HTTP requests. They will be automatically redirected to HTTPS;
- Delete IP adresses — activate the option to remove all addresses that are listening on the specified port.
Panel address certificates
Let’s Encrypt certificate
This feature is supported from version 5.124.
Let’s Encrypt is a free certification authority that provides free X.509 certificated for TLS encryption. An automated process enables to facilitate the creation, verification, setup, and renewal of SSL certificates for protected websites.
For more information, please refer to the official website.
Please note the following limits
- You can order only 5 certificates a week (TLD, including its subdomains)
- Wildcard certificates are not supported
- Let’s Encrypt certificate validity period is 3 months (every 3 months ISPmanager will reissue Let’s Encrypt certificates)
More information about additional limits can be found here.
Before you add Let’s Encrypt certificate, make sure that the domain name leads to existing IP address of the control panel, as the system will verify that you are the owner of that domain.
A file with token and data for verification is created in
/usr/local/mgr5/www/letsencrypt/.well-known/acme-challengeLet’s Encrypt sends a request by the domain name and reads the token.
After the certificate is issued, a new cron job is added. It will check if the certificate needs to be renewed:
0 0 * * * "/usr/local/mgr5/etc/scripts/acmesh"/acme.sh --cron --home "/usr/local/mgr5/etc/scripts/acmesh" > /dev/null
If several certificates for 3d-level (and higher) domain names are issued, you may face the "Too many subdomains" error. This Let’s Encrypt restriction allows to continue the issue procedure after a while (normally, within 24 hours).
Apache and Nginx web-servers are supported. If none of these servers are running, a built-in server will start to receive requests from Let’s Encrypt during domain verification.
Existing certificate
When you add an existing certificate, domain name and its IP address are not checked. If domain and IP address do not match, the corresponding icon will be shown next to the certificate.
- Certificate type — select a certificate that you want to order.
- Let’s Encrypt certificate
- Existing certificate
- Domain name — enter a domain name the certificate will be issued for. If you want to use an existing SSL-certificate, the domain name will be taken from that certificate.
- IP address — IP address of the control panel that will be associated with the certificate.
- SSL-certificate — enter an SSL-certificate you want to use.
- SSL-certificate key — enter a key for your certificate
- SSL-certificate chain — enter a certificate chain that will be added into the certificate file.
Server Name Indication
If OS supports Server Name Indication, you can add several SSL-certificates for different domain names. When you access a panel via domain name, the panel will use the certificate corresponding to that domain name.
Server Name Indication is supported by:
- CentOS 7 and later.
- Debian 8 and later.
- Ubuntu16.04 and later.
Certificates with alternative domain names are also supported.
Delete address
To delete an address, select it from the list and click the Delete icon. Confirm that you want to delete the selected address by clicking OK in the following window.